|
“Uncommon Carriers”, The Orange County Register, April 4, 2010. Larry’s op-ed in the Register points out some of the reasons why Internet access has fared so well without FCC oversight, while traditional phone service has languished. |
Monthly Archives: June 2010
Examiner/eBay v Tiffany's
| “Another win for eBay and e-Commerce”, Examiner.com, April 2, 2010. Larry is interviewed on eBay’s win in the Second Circuit in its on-going disputes with Tiffany’s over who is responsible for counterfeit and gray-market goods that eBay sellers offer. |
The Fallacy of “e-personation” Laws
 I was interviewed yesterday for the local Fox affiliate on Cal. SB1411, which criminalizes online impersonations (or “e-personation”) under certain circumstances.
I was interviewed yesterday for the local Fox affiliate on Cal. SB1411, which criminalizes online impersonations (or “e-personation”) under certain circumstances.
On paper, of course, this sounds like a fine idea. As Palo Alto State Senator Joe Simitian, the bill’s sponsor, put it, “The Internet makes many things easier. One of those, unfortunately, is pretending to be someone else. When that happens with the intent of causing harm, folks need a law they can turn to.”
Or do they?
The Problem with New Laws for New Technology
SB1411 would make a great exam question of short paper assignment for an information law course. It’s short, is loaded with good intentions, and on first blush looks perfectly reasonable—just extending existing harassment, intimidation and fraud laws to the modern context of online activity. Unfortunately, a careful read reveals all sorts of potential problems and unintended consequences.
A number of states have passed new laws in the wake of highly-publicized cyberstalking and bullying incidents, including the tragic case involving a young girl’s suicide after being dumped by her online MySpace boyfriend, who turned out to be a made-up character created for the purpose of hurting her feelings. (I’ve written about the case before, see “Lori Drew Verdict Finally Overturned.” )
Missouri passed a cyberbullying law when it turned out there was no federal law that covered the behavior in the MySpace case. Texas and New York recently enacted laws similar to SB 1411, though the Texas law applies only to impersonation on social media sites.
The problem with all these laws generally is that the authors aren’t clear what behaviors exactly they are trying to criminalize. And, mindful of the fact that the evolution of digital life is happening much faster than any legislative body can hope to keep up with, these laws are often written to be both too specific (the technology changes) and too broad (the behavior is undefined). As a result, they often don’t wind up covering the behavior they intend to deter, and, left on the books, can often come back to life when prosecutors need something to hang a case on that otherwise doesn’t look illegal.
Given the proximity to free speech issues, the vagueness of many of these laws makes them good candidates for First Amendment challenges, and many have fallen on that sword.
California’s SB 1411 as a Case in Point
SB1411, which last week passed in the State Senate, suffers from all of these defects. It punishes the impersonation of an “actual person through or on an Internet Web site or by other electronic means for purposes of harming, intimidating, threatening or defrauding another person.” It requires the impersonator to knowingly commit the crime and do so without the consent of the person they are imitating. It also requires that the impersonation be credible. Punishment for violation can include a year in jail and a suit brought by the victim for punitive damages.
First let’s consider a few hypotheticals, starting with the one that inspired the law, the MySpace case noted above. Since the boy whose profile lured the victim into an online romance that was then cruelly terminated was a made-up person (the perpetrators found some photo of a suitably shirtless teen and built a personality around it), SB 1411 would not apply had it been the law in Missouri. The boy was not an “actual person,” and, except perhaps to a thirteen year old with existing mental health problems, may not have been credible either. (The determination of “credibility” under SB 1411 would presumably be based on the “reasonable person” standard.) Likewise, law enforcement agents creating fake Craigslist ads to smoke out drug buyers, child molesters, or customers of sex workers would also not be violating the law.
Also excluded from SB 1411 would probably be those who use Craigslist to get back at exes or other people they are angry at by placing ads promising sex to anyone who stops by, and then gives the address of the person they are trying to get even with. In most cases, these ads are not credible impersonations of the victim; they are meant to offend them but not to convince a reasonable third person that they really speak for the victim. A fake Facebook page for a teacher who proceeds to make cruel or otherwise harmful statements about her students, likewise, would not be a credible impersonation.
The Twitter profiles being created to issue fake press releases purportedly on behalf of BP would also not be illegal under SB 1411. First, BP is not an “actual person.” Second, Twitter profiles such as BPGlobalPR are clearly parodies—they are issuing statements they believe to be what BP would say if it were telling the truth about its actions in relation to the gulf spill. (“We’re on a seafood diet- When we see food, we eat it! Unless that food is seafood from the Gulf. Yuck to that.”) Again, not a credible impersonation.
You also do not commit the crime by confusing people inadvertently. There are several people I am aware of online named Larry Downes, including a New Jersey state natural resources regulator, a radio station executive and conservative commentator, a cage fighter and a veterinarian who lives in a nearby community. (The latter is a distant cousin.) Facebook alone has 11 profiles with my name. Only one of them is actually me, but the others are not knowingly impersonating me just because they use the same name, even if some third person might be confused to my detriment.
Likewise, the statute doesn’t reach out to those who help the perpetrator, intentionally or otherwise. The “Internet Web sites” or providers of other electronic means aren’t themselves subject to prosecution or civil cases brought by the victims of the impersonation. So Craigslist, MySpace, Facebook, and Twitter aren’t liable here, nor are the ISPs of the perpetrators, even if made aware of the activity of their users and/or customers.
For one thing, a federal law, Section 230, immunizes providers against that kind of liability under most circumstances. Last week, Craigslist lost its bid to preclude a California lawsuit using Section 230 as its defense when sued by the victim of fake posts soliciting sex and offering to give away his possessions. The victim informed Craigslist of the problem, and the company promised to take action to stop future posts but did not succeed. But it lost its immunity only by promising to help which, of course, the site won’t do in the future! (See Eric Goldman’s analysis of the case.)
So there are important limitations (some added through recent amendments) to SB 1411 that reduce the possibility of its being applied to speech that is otherwise protected or immunized by federal law. (In the BP example, the company might have a trademark case to bring.) Most of these limits, however, seem to take any teeth out of the statute, and seem to exclude most of the behavior Sen. Simitian says he is concerned about.
Unintended Consequences
What’s left? Imagine a case where, angry at you, I create a fake Facebook profile that purports to represent you. I post material there that is not so outrageous that the impersonation is no longer credible, but which still has the intent of harming, intimidating, threatening or defrauding you. Perhaps I report, pretending to be you, about all of my extravagant purchases (but not so extravagant that I am not credible), leading your friends to believe you are spending beyond your means. You find out, and find my actions intimidating or threatening.
Perhaps I announce that you have defaulted on your mortgage and are being foreclosed, leading your creditors to seek security on your other debts. Perhaps I threaten to continue posting stories of your sexual exploits, forcing you to pay me blackmail to save you embarrassment.
Would these cases be covered under SB 1411? Perhaps, unless of course the claims that I am making as you turn out to be true. In the U.S., truth is a defense to defamation, so even if my intent is to “harm” you by revealing these facts, if they are facts then there is no action for defamation. That I say the facts pretending to be you, under SB 1411, would appear to turn a protected activity into a crime, perhaps not what the drafters intended and perhaps not something that would stand up in court. (The truth-as-defense in defamation cases rests on First Amendment principles—you can’t be prosecuted for saying the truth.)
Of course, much of the other behavior I described above is already a crime in California—in particular, various forms of intimidation, harassment and, by definition, fraud. The authors of SB 1411 believe the new law is needed to extend those crimes to cover the use of “Internet Web sites” and “other electronic means,” but there’s no reason to believe that the technology used is any bar to prosecutions under existing law. (Indeed, the use of electronic communications to commit the acts would extend the possible criminal laws that apply, since electronic communications are generally considered interstate commerce and thus subject to federal as well as state laws.)
For the most part, then, SB 1411 covers very little new behavior, and little of the behavior its drafters thought needed to be criminalized. For an impersonation to be damaging would, in most cases, mean that it was also not credible. Pretending to be me and telling the truth could be harmful, but probably a form of protected speech. Pretending to be me in order to defraud a third party is already a crime-that is the crime of identity theft.
Which is not to say, pun intended, that the proposed law is harmless. For in addition to categories of behavior already covered by existing law, SB 1411 makes it a crime to impersonate someone with the purpose of “harming” “another person.” There is, not surprisingly, no definition given for what it means to have the purpose of “harming,” nor is it clear if “another person” refers only to the person whose identity has been usurped, or includes some third party (perhaps a family member or friend of that person, perhaps their employer.)
Having a purpose of “harming” “another person” is incredibly vague, and can cover a wide range of behaviors that wouldn’t, in offline contexts, be subject to criminal prosecution. The only difference would be that the intended harm here would be operationalized through online channels, and would take the form of a credible impersonation of some actual person.
Why those differences ought to result in a year in jail doesn’t make much sense. Consequently, an attempt to use the law to prosecute “harmful” behavior would be met with a strong constitutional objection.
That’s my read of the bill, in any case. Since I posed this as an exam question, I’m offering extra credit for anyone who can come up with examples—there are none given by the California State Senate—of situations where the law would actually apply and that would not already be illegal and which would not be subject to plausible Constitutional challenges.
The Privacy and Security Totentanz
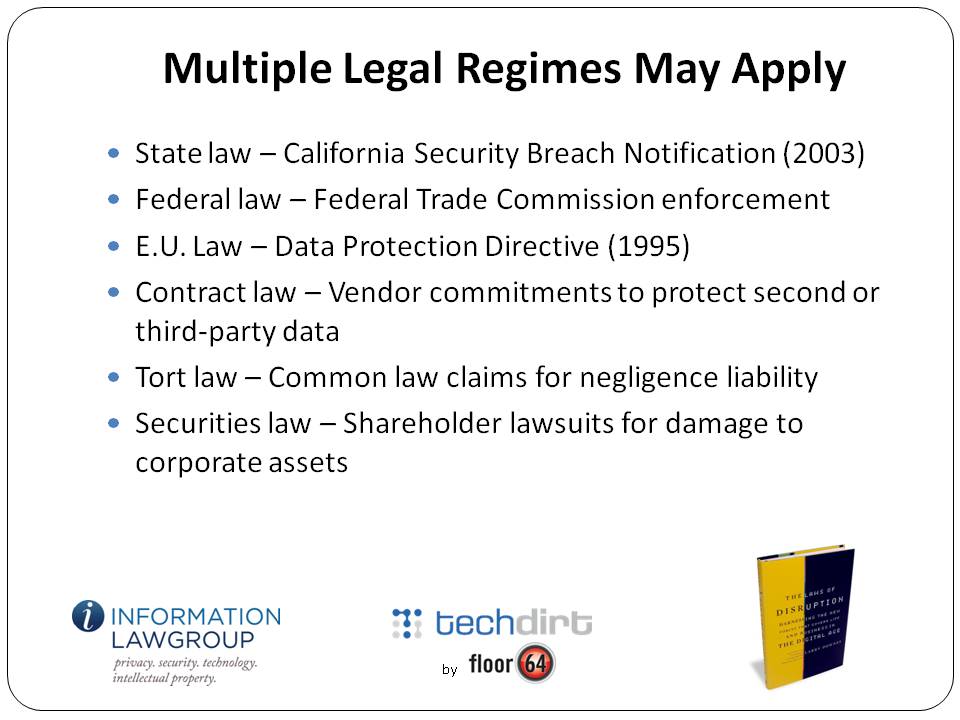
I participated last week in a Techdirt webinar titled, “What IT needs to know about Law.” (You can read Dennis Yang’s summary here, or follow his link to watch the full one-hour discussion. Free registration required.)
The key message of The Laws of Disruption is that IT and other executives need to know a great deal about law—and more all the time. And Techdirt does an admirable job of reporting the latest breakdowns between innovation and regulation on a daily basis. So I was happy to participate.

Legally-Defensible Security
Not surprisingly, there were far too many topics to cover in a single seminar, so we decided to focus narrowly on just one: potential legal liability when data security is breached, whether through negligence (lost laptop) or the criminal act of a third party (hacking attacks). We were fortunate to have as the main presenter David Navetta, founding partner with The Information Law Group, who had recently written an excellent article on what he calls “legally-defensible security” practices.
I started the seminar off with some context, pointing out that one of the biggest surprises for companies in the Internet age is the discovery that having posted a website on the World Wide Web, they are suddenly and often inappropriately subject to the laws and jurisdiction of governments around the world. (How wide is the web? World.)
In the case of security breaches, for example, a company may be required to disclose the incident to affected third parties (customers, employees, etc.) under state law. At the other extreme, executives of the company handling the data may be criminally-liable if the breach involved personally-identifiable information of citizens of the European Union (e.g., the infamous Google Video case in Italy earlier this year, which is pending appeal). Individuals and companies affected by a breach may sue the company under a variety of common law claims, including breach of contract (perhaps the violation of a stated privacy policy) or simple negligence.
The move to cloud computing amplifies and accelerates the potential nightmares. In the cloud model, data and processing are subcontracted over the network to a potentially-wide array of providers who offer economies of scale, application or functional expertise, scalable hardware or proprietary software. Data is everywhere, and its disclosure can occur in an exploding number of inadvertent ways. If a security breach occurs in the course of any given transaction, just untangling which parties handled the data—let alone who let it slip out—could be a logistical (and litigation) nightmare.
The Limits of Negligence
Not all security breaches involve private or personal information, but it’s not surprising that the most notable breakdowns (or at least the most vividly-reported) in security are those that expose consumer or citizen data, sometimes for millions of affected parties. (Some of the most egregious losses have involved government computers left unsecured, with sensitive citizen data unencrypted on the hard drive.) Consumer computing activity has surpassed corporate computing and is growing much faster. Privacy and security are topics that are increasingly hard to disentangle
Which is not to say that the bungling of data that affects millions of users necessarily translates to legal consequences for the company who held the information. Often, under current law, even the most irresponsible behavior by a data handler does not necessarily translate to liability.
For one thing, U.S. law does not require companies to spare no expense in protecting data. As David Navetta points out, courts may find that despite a breach the precautions taken may have nonetheless been economically sensible, meaning that the precautions taken were justified given the likelihood of a breach and the potential consequences that followed. Adherence to ISO or other industry standards on data security may be sufficient to insulate a company from liability—though not always. (Courts sometimes find that industry standards are too lax.)
For the most part, tort law still follows the classic negligence formula of the beatified American jurist Learned Hand, who explained that the duty of courts was to encourage behavior by defendants that made economic sense. If courts found liability any time a breach occurred, then data handlers would be incentivized to spend inefficient amounts of money on protecting it, leading to net social loss. (The classic cases involved sparks from locomotives causing fire damage to crops—perfect avoidance of damage, the courts ruled, would cost too much relative to the harm caused and the probability of it occurring.)
That, at least, is the common law regime that applies in the U.S. The E.U., under laws enacted in support of its 1995 Privacy Directive, follow a different rule, one that comes closer to product liability law, where any failure leads to per se liability for the manufacturer, or indeed for any company in the chain of sales to a consumer.
A case last week from the Ninth Circuit Court of Appeals, however, reminds us that a finding of liability doesn’t necessarily lead to an award of damages. In Ruiz v. Gap, a job applicant whose personal information was lost when two laptop computers were stolen from a Gap vendor who was processing applications sued Gap, claiming to represent a class of applicants who were victims of the loss.
All of Ruiz’s claims, however, were rejected. Affirming the lower court and agreeing with most other courts to consider the issue, the Ninth Circuit held that Ruiz could not sue Gap without a showing of “appreciable and actual damage.” The cost of forward-looking credit monitoring didn’t count (Gap offered to pay Ruiz for that in any case), nor did speculative claims of future losses. Actual losses, expressible and provable in monetary terms, were required.
The court also rejected claims under California state law and the state constitution, noting that an “invasion of privacy” does not occur until there is actual misuse of the data contained on the stolen laptops. (Most laptop thefts are presumably motivated by the value of the hardware, not any data that might reside on the hard drive.)
As Eric Goldman succinctly points out, the Ninth Circuit case highlights some odd behavior by plaintiff class action lawyers in the recent hubbub involving Facebook, Google, and other companies who either change their privacy policies or who use customer data in ways that arguably violate that policy. “[T]he most disturbing thing,” Eric writes, “is that so many plaintiffs’ lawyers seem completely uninterested in pleading how their clients suffered any consequence (negative or otherwise) from the gaffe at all. Their approach appears to be that the service provider broke a privacy promise, res ipsa loquitur, now write us a check containing a lot of zeros.”
A Surprising Lack of Law – And an Alternative Model for Redress
It’s not just the lawyers who are confused here. U.S. consumers, riled up by stories in mainstream media, seem to live under the misapprehensions that they have some legal right to privacy, or that the protection of personal information that can be enforced in courts against corporations.
That is true in the E.U., but not in the U.S. The Constitutional “right to privacy” detailed in U.S. Supreme Court decisions of the last fifty years only applies to protections against government behavior. There is no Constitutional right to privacy that can be enforced against employers, business partners, corporations, parents, or anyone else.
What about statutes? With a few specific exceptions for medical information, credit history, and a few other categories, there is also no U.S. or for the most part state law that protects consumer privacy against corporations. There’s no law that requires a website to publish its privacy policy, let alone follow it. Even if policy constitutes an enforceable contract (not entirely a settled matter of law), the Ruiz case reminds us that breach of contract is irrelevant without evidence of actual monetary damages.
Before storming the barricades demanding justice, however, keep in mind that the law is not the only source of a remedy. (Indeed, law is rarely the most efficient or effective in any case.)
The lack of a legal remedy for misuse of private information doesn’t mean that companies can do whatever they like with data they collect, or need take no precautions to ensure that information isn’t lost or stolen.
As more and more personal and even intimate data migrates to the cloud, it has become crystal-clear that consumers are increasingly sensitive (perhaps, economically-speaking, over-sensitive) about what happens to it. Consumers express their unhappiness in a variety of media, including social networking sites, blogs, emails, and tweets. They can and do put economic pressure on companies whose behavior they find unacceptable: boycotts, switching to other providers, and through activism that damages the brand of the miscreant.
Even if the law offers no remedy, in other words, the court of public opinion has proven quite effective. Even without a court ordering them to do so, some of the largest data handlers have made drastic changes to their policies, software, and how they communicate with users.
Looming in the background of these stories is always the possibility that if companies fail to appease their customers, the customers will lobby their elected representatives to provide the kind of legal protections that so far haven’t proven necessary. But given the mismatch between the pace of innovation and the pace of legal change, legislation should always be the last, not the first, resort.
So expect lots more stories about security breaches, and expect most of them to involve the potential disclosure of personal information. (That’s one reason that laws requiring disclosure of breaches are a good idea. Consumers can’t flex their power if they are kept in the dark about behavior they are likely to object to.)
And that means, as we conclude in the seminar, that IT executives making security decisions had better start talking to their counterparts in the general counsel’s office.
Because as hard as it is for those two groups to talk to each other, it’s much harder to have a conversation after a breach than before. IT makes decisions that affect the legal position of the company; lawyers make decisions that affect the technical architecture of products and services. The question isn’t whether to formulate a legally-defensible security policy, in other words, but when.